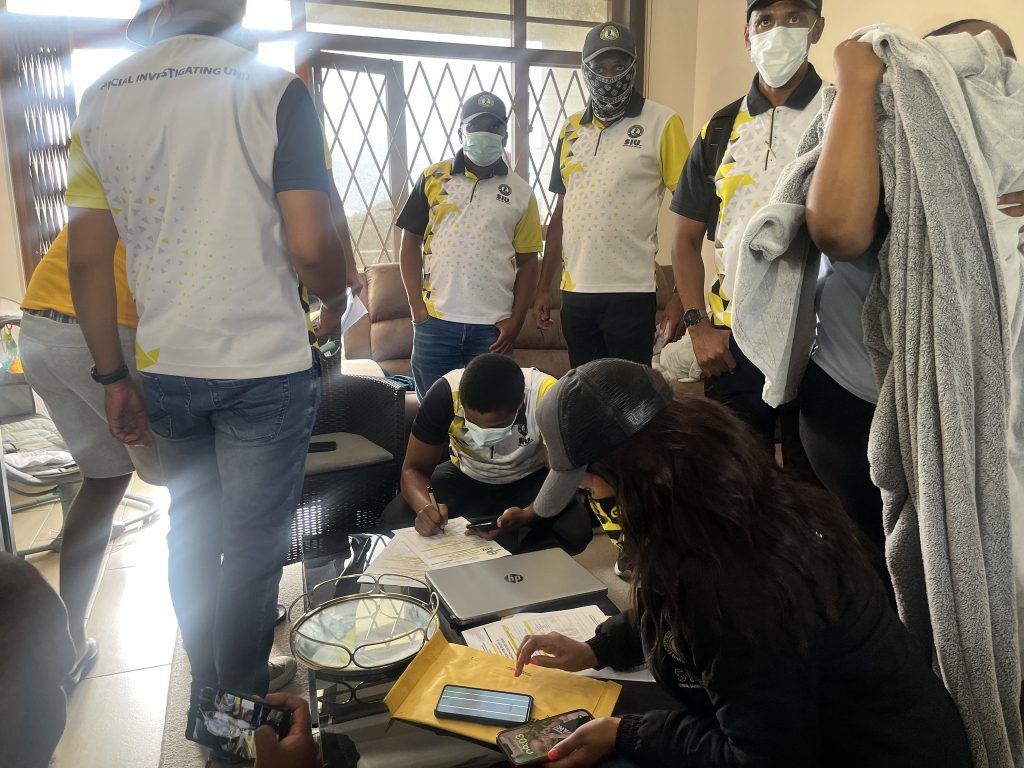
In a massive crackdown on pandemic-era corruption, the Special Investigating Unit (SIU) and specialised police units launched a coordinated search and seizure operation across KwaZulu-Natal and Gauteng on Thursday 11 December, targeting a sophisticated syndicate accused of looting approximately R161 million from the Unemployment Insurance Fund (UIF).
The operation, which began at dawn, targets a network of 16 companies and over 35 individuals alleged to have siphoned funds meant for workers during the Covid-19 lockdown. Among the high-profile targets identified by investigators is a sitting local councillor in the Ray Nkonyeni Municipality and a businessman alleged to be the syndicate’s “mastermind”.
The raids are being executed under the authority of a warrant issued by Judge M. Victor of the Special Tribunal on 10 December. The warrant authorises investigators to enter premises, search for, and seize evidence related to the massive fraud scheme.
Due to the scale and sophistication of the alleged criminal enterprise, the SIU is supported by elite units of the South African Police Service (SAPS), including the National Intervention Unit (NIU), Tactical Response Team (TRT), and the Directorate for Priority Crime Investigation (the Hawks).
Teams simultaneously descended on luxury residences and business premises in Sandton, Fourways, Pietermaritzburg, Port Shepstone, and the UIF Head Office in Pretoria. The search warrant explicitly lists three categories of targets: companies and their directors, specific persons of interest, and internal UIF officials suspected of collusion.
Central to the investigation is Nhlakanipho Mngomezulu, a director of Lubelo Hlomuka Holdings trading as SA Scrum Assembly. The SIU has identified Mngomezulu as the alleged “mastermind” of the operation, known within the syndicate by the alias “Mkhulu”. His company alone reportedly received R15,917,398.98 in fraudulent Temporary Employer/Employee Relief Scheme (Ters) funds. Investigators are currently combing through associated addresses in Pietermaritzburg, Durban, and upmarket suburbs in Johannesburg in search of digital and paper trails linking him to the theft.
In a significant political development, the raids also targeted Thamsanqa Madlala, a director of Bokoharama Construction and a local councillor at the Ray Nkonyeni Municipality in KwaZulu-Natal. Madlala is described as a “key person of interest”. His company allegedly received R18,197,289.94 from the relief fund.
‘Millions not used for business relief or worker salaries’
According to the SIU, the investigation has revealed that the millions paid into Madlala’s company accounts were not used for business relief or worker salaries. Instead, the funds were allegedly channelled toward purchasing assets for the syndicate’s leadership and other figures involved in the scheme.
The investigation, authorised under Proclamation R8 of 2021, paints a picture of a “well-organised” criminal enterprise. The syndicate allegedly orchestrated the submission of false applications to the Covid-19 Ters.
These applications were filed on behalf of individuals who were never employed by the applicant companies. Once the substantial funds were paid out by the UIF, they were not distributed to the “workers” listed in the applications.
The money was quickly moved and distributed among syndicate members in complex patterns consistent with money laundering.
The network relied on a web of proxies and “runners” to move the cash. The SIU has identified individuals such as Sphamandla Sokhela and attorney Nhlakanipho Zondi as alleged proxies for Mngomezulu. Furthermore, Senzo Gumede, director of Amakhosana Contractors and Senzisipho Pty Ltd, is being investigated for using his companies to launder the stolen funds.
Other significant amounts uncovered during the probe include R19,183,197.34 paid to Nakomang Trading Enterprise in Gauteng and R3.8 million paid to Aventador Gate in Pretoria. Another key figure, Yolanda Nombuso Mgobo, is alleged to have received and distributed over R18.6 million in illicit funds.
Several UIF officials probed for possible involvement
Perhaps most concerning for the Department of Employment and Labour is the simultaneous raid on the UIF Head Office at 230 Lillian Ngoyi Street in Pretoria. The SIU suspects that the external syndicate could not have operated so successfully without internal assistance.
Investigators are probing several UIF officials for their possible involvement. These officials are suspected of facilitating the fraudulent applications, bypassing audit processes, and manipulating the UIF’s digital systems to clear “victim” profiles, likely to prevent the fraud from being flagged by automated security checks.
The search warrant authorises the seizure of internal correspondence, memoranda of understanding (MOUs), and digital logs that could prove how the syndicate bypassed the fund’s verification systems.
The primary objective of the operation is to secure evidence that might otherwise be destroyed. The search warrant grants investigators broad powers to seize computers, laptops, data storage devices, and mobile phones.
Investigators are also looking for original bank statements and fraudulent Ters application documents. The seized items will undergo immediate forensic analysis to trace the flow of money and cement the link between the alleged fraudsters and the stolen millions.
The SIU has stated that the evidence gathered will be used for two primary purposes: to institute civil litigation to recover the financial losses suffered by the state, and to build criminal dockets.






You must be logged in to post a comment.